Blocking via Hosts File: 100% Solid Tips
[ad_1]
You might have heard of the hosts file. If not, you didn’t miss much. Literally, that’s a computer file with “hosts” as the name. It has no extension that determines what type of file it is.
So, the file itself is inconsequential. However, when placed at a particular location within your computer, it can be an effective tool to control a computer’s access to the outside world, a.k.a the Internet. In this case, I’d refer to it as the hosts file (cue spooky music).
If you’re interested in a simple and effective way to block certain websites from a computer, or simply want to know what sorcery this is, you’re reading the right post. I’ll explain how to manage the host file on your computer, be it a Windows or a Mac — if you use any other platform, such as Linux, you’d know what to do.

What is the host file, and how to handle it
Every computer running Windows, macOS, or Linux has its hosts file. By default, this file is not in effect. It’s there but it doesn’t do anything other than containing some information explaining briefly what it is and how to use it.
In other words, you can delete the default hosts file, and nothing will happen. We don’t need it. And we can always recreate it.
Understanding the Hosts file
When edited in a certain way, the hosts file works as the computer’s local DNS mapper — or directory. It’s a manual way to map a domain, such as facebook.com, to a particular IP address of your choosing.
(It’s the old way of binding a domain with an IP address in the early days of inter-connected computers, the foundation of the Internet, before the DNS server came into existence.)
So, when you map a domain to a non-existing IP address or that of the computer itself, you effectively block the domain for the computer’s users.
The hash sign (#) in a hosts file signifies commenting.
In programming, commenting is a way to explain what a line of code does without affecting the code itself. The computer ignores the # symbol itself and the text that follows it on each line.
If a hosts file has # at the beginning of every line, which is the default, it’s as good as a blank file from the computer’s perfective.
Here’s an example of an entry in a hosts file:
127.0.0.1 facebook.comThe format of the line above is known as the command syntax. In this case, it’s:
IP address (space) domain
(We only need a single space to separate the IP address and the domain, but for clarity, I hit the spacebar a few times — you can also use the Tab key on the keyboard.)
This particular entry points facebook.com to the IP of the localhost, the computer itself, and in effect, blocks the computer’s access to Facebook. Specifically, when you go to facebook.com, you’ll get a message that the website doesn’t exist or is unavailable.
Alternatively, you can also use 0.0.0.0 as the IP address to get the same effect. And if you use the IP address of another website or server, the entry becomes a mean prank or a malicious hack.
This mapping takes effect system-wide and immediately — generally, there’s no need to restart the computer.
The way it works, every time you want to reach a domain, such as entering it on a browser, the computer will check its hosts file for the mapping, and if the domain is manually mapped, it’ll use that and no longer query a DNS server for that domain.
A DNS server is like a public directory of the Internet. It points you to where you want to go. (This is not to be confused with Dynamic DNS, which works somewhat the opposite way.)
Here’s a typical example of the role DNS plays:
Whenever you access a website, such as dongknowstech.com, which is a domain name, the browser — Chrome, Firefox, Edge, etc. — first query your DNS server, set by your home router.
This server then looks up the website’s domain name (a.k.a. web address or URL) and returns its IP address — a string of seemingly random numbers — to the browser. (Every website has an IP address.) The browser then follows that IP address to load the website.
This process is necessary because computers only understand numbers while humans are pretty bad at remembering them.
So a DNS server is similar to the (once commonplace) telephone directory service where you only need to remember a person’s name and not their phone number.
And you can manually map as many domains as you’d like — as long as you know what you’re doing and don’t abuse it.
Each mapping entry (each domain) takes one line within the hosts file. You can map multiple domains to the same IP address. So use 0.0.0.0 or 127.0.0.1 if you want to block all of them.
With that, let’s find out where this glorious hosts file resides on your computer and how to edit it.
How to handle the host file on a Windows computer
On a Windows computer, the Hosts file always resides at this location:
c:\windows\system32\drivers\etc\(In the rare case where Windows is installed on another drive instead of c:, change the drive letter accordingly.)
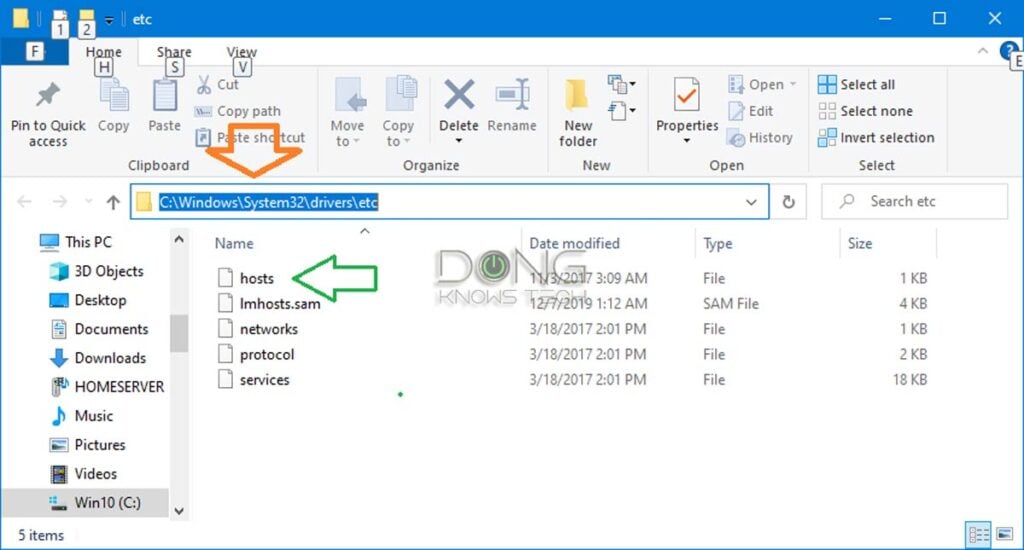
Copy and paste that line onto the address bar of Windows Explorer and hit Enter to quickly get there, as shown in the screenshot above.
Now you can manage the file however you do any file, including deleting, renaming, or making a copy of it. By the way, if you move the host file to another location, it no longer has any effect.
It takes a bit of work to open the host file for editing. Since it has no extension, the usual double-clicking won’t do. But you can open it the way you open any file using a text editor, such as Windows’s built-in Notepad app.
If you’re unfamiliar with the app or don’t know how to handle files in general, the fastest way to open the hosts for editing in Windows is to copy and paste the command below on the address bar of Explorer, then hit Enter (screenshot below):
notepad c:\windows\system32\drivers\etc\hosts
That will open the file in Notepad for you to make any changes. Again, you can add one domain per line, as shown in the screenshot (the last two lines). Once done, save the file — use the Ctrl+S keyboard combo, or close the file and choose to save when prompted.
Mission accomplished.
By the way, the host file shares the same syntax across platforms. Consequently, you can use the same file between Windows and macOS. Or you can copy the content of the file between them.
How to handle the host file on a Mac
The hosts file is located in the /private/etc/ folder on a Mac, which is generally hidden.
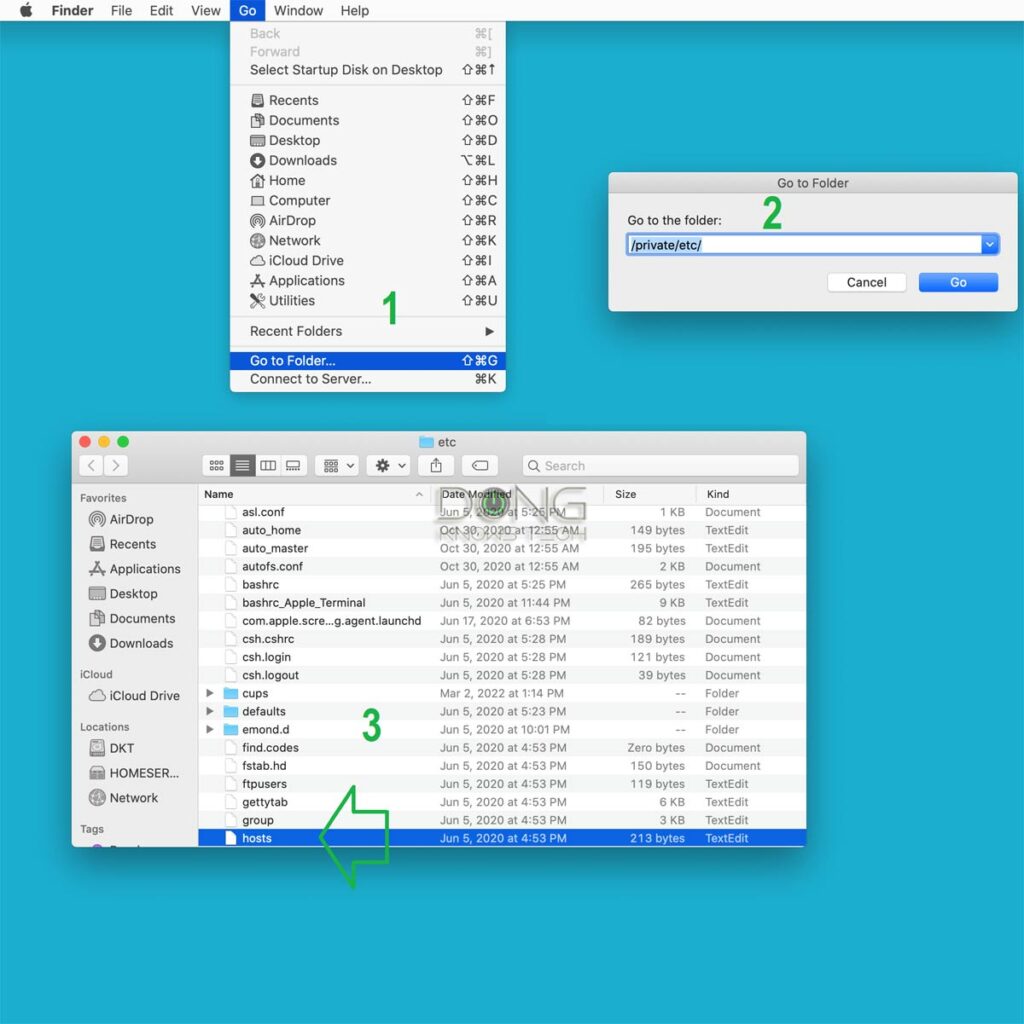
Here are the steps to locate the hosts file on a Mac, as shown in the screenshot above:
- Bring Finder to the forefront by clicking on a blank spot on the desktop, then choose Go -> Go to Folder…
- Enter /private/etc/ in the field and hit Go.
- Locate the host file in the folder that appears. If it’s not there (unlikely), you can make a new one or copy one over from another computer.
But if you want to edit the file, you can skip the above.
Here are the step to open the host file on a Mac for editing
- Run Terminal (use the Spotlight to search for it) and enter the following command, and press Enter:
sudo nano /etc/hostsYou’ll be asked to enter the password for the account. Do it!

2. The hosts file will be open in the Nano app. You can now use the arrow key to move around and enter the information as needed.
After that, use Ctrl+0 to save the changes and Ctrl+X to exit.
Mission accomplished.
Not a security measure
Before using the host’s file for blocking purposes, ask yourself why you want to block a domain instead of just not visiting it.
No matter your answer, this blocking mechanism applies when you want to exert control over something you don’t have (enough) control over.
Here are examples:
- You want to practice real Parental Control over your child’s online life.
- When you want to give yourself a cushion in controlling the urge to visit websites that you know you shouldn’t.
- You just want to mess with, or impress somebody.
The point is the hosts file is not a security measure, it’s a control measure. Blocking a domain doesn’t make your computer any safer. It only limits what the machine can access. (And it doesn’t limit the remote party in accessing your network.)
By the way, if I know about the hosts file, which you now do, too, we have to assume that the bad guys also know it. As a result, keep in mind that the file can be used for no-good purposes, considering how easy it is to alter it.
The final thoughts
Using the hosts file can be a sure and straightforward way to block certain websites from a computer. But entering one domain at a time into the hosts file can be time-consuming. For this reason, there are a lot of pre-made hosts files where somebody has compiled a long list of blocked domains.
However, be careful with these pre-packaged hosts files. They tend to include hundreds of domains to block all kinds of things, including legit services. That’s not to mention there can be malicious entries.
Many domains are interconnected — blocking one might cause others not to work properly. Blocking a wrong domain can also cause important functions of a computer, such as auto-updates or security/integrity checks, to stop working.
On top of that, a large hosts file can also cause performance issues. It’s a good idea to keep its size below a few hundred kilobytes.
In short, the hosts file is a good tool when you use it properly, for the right purpose. But it can also be a pain when you abuse it. I’d only use it only when I enter specific domains I want to block.
In any case, it’s a good practice to be mindful of this file’s existence. Also, use a blank (default) hosts file when troubleshooting your connection. And worse comes to worst, remember that you can always safely delete this file or move it away from the default location. It’s not an essential part of a system.
[ad_2]
Source link







